Category:Computer security
Przejdź do nawigacji
Przejdź do wyszukiwania
English: Computer security, also known as cyber security or IT security, is the protection of computer systems from the theft or damage to their hardware, software or information, as well as from disruption or misdirection of the services they provide.
ochrona systemów i sieci komputerowych przed kradzieżą, uszkodzeniem lub wyciekiem danych | |||||
| Prześlij plik multimedialny | |||||
| Jest to |
| ||||
|---|---|---|---|---|---|
| Podklasa dla | |||||
| Część |
| ||||
| Składa się z | |||||
| Uważa się za to samo co | cyberbezpieczeństwo, cyberbezpieczeństwo | ||||
| |||||
Podkategorie
Poniżej wyświetlono 49 spośród wszystkich 49 podkategorii tej kategorii.
*
+
A
- Aura (Information protection system) (3 pliki)
B
- BullGuard (software) (3 pliki)
C
D
- Demilitarized zones (computing) (2 pliki)
E
- Evil twin (wireless networks) (4 pliki)
H
- Hardware security modules (10 plików)
- Heartbleed bug (16 plików)
I
- IT Baseline Protection Catalogues (5 plików)
J
- Java Anon Proxy (1 plik)
K
- Keystroke logging (16 plików)
L
M
- Meltdown (4 pliki)
N
- Niksun (24 pliki)
O
- Openwall project (4 pliki)
R
S
- SecurityMetrics (5 plików)
T
- Take-grant protection model (6 plików)
- Threat (computer) (7 plików)
- Trusted Execution Technology (4 pliki)
U
- Unam cert (17 plików)
V
- Verinice (2 pliki)
W
- Webroot (11 plików)
Pliki w kategorii „Computer security”
Poniżej wyświetlono 200 spośród wszystkich 372 plików w tej kategorii.
(poprzednia strona) (następna strona)-
12.11「106年府會資安週」工作人員模擬駭客入侵監控系統 (27199749569).jpg 2048 × 1365; 1,8 MB
-
Cybersecurity and the nation's digital future.jpg 3500 × 2333; 779 KB
-
2015-10-05 experian-letter-redacted.jpg 2574 × 3531; 1,73 MB
-
2022 ITRC Logo Color Horizontal.png 5942 × 1650; 70 KB
-
2Q15 Transaction - Protecting Your Children's Credit.pdf 1275 × 1650, 2 strony; 222 KB
-
3wPlayer.jpg 517 × 405; 97 KB
-
4300 side.jpg 3164 × 1052; 745 KB
-
A Hacker Works at a COmputer in a Dark Room.png 5824 × 3264; 18,47 MB
-
Aaaasss.png 300 × 192; 17 KB
-
ACARM-ng architecture.png 1626 × 1032; 172 KB
-
ACARM-ng logo.svg 183 × 85; 35 KB
-
ACARM-ng WUI alert time series 1.png 948 × 548; 60 KB
-
ACARM-ng WUI sample alert 1.png 948 × 548; 86 KB
-
Access Control List of Dokuwiki.jpg 928 × 565; 137 KB
-
Aircrack-ng.png 626 × 413; 6 KB
-
ANSSI.jpg 410 × 120; 18 KB
-
Application Threat Model PFD.jpg 842 × 440; 82 KB
-
Approaches to privacy and security in computer systems (IA approachestopriv404renn).pdf 1064 × 1441, 88 stron; 6,23 MB
-
APT28 APT29 Techniques - Malware.png 1431 × 805; 192 KB
-
APT28 APT29 Techniques - Spearphising.png 1431 × 805; 234 KB
-
Arm partial screenshot.png 400 × 250; 76 KB
-
Array for spraying.jpg 621 × 829; 149 KB
-
Artists Against 419 - Fake Sites Database detail page.png 1262 × 1319; 286 KB
-
Artists Against 419 - Fake Sites Database index page.png 1262 × 1137; 313 KB
-
Aslr stack smash.svg 743 × 227; 36 KB
-
Attaque par relais sur le protocole Echo.png 419 × 503; 36 KB
-
Attaques.png 633 × 488; 67 KB
-
AusweisApp.png 674 × 480; 45 KB
-
Autentificare vs autorizare.PNG 717 × 485; 40 KB
-
Auth ssh.png 639 × 311; 11 KB
-
Bingo-Card.png 1176 × 767; 106 KB
-
Bitdefender Awards.jpg 4397 × 3298; 2,59 MB
-
Bitdefender Headquarters Bucharest Romania.jpg 3977 × 2237; 1,25 MB
-
Black Channel Prinzip.PNG 412 × 337; 15 KB
-
BlackHoleAttack.jpg 815 × 568; 68 KB
-
Bleib wachsam Darmstadt.png 2743 × 1200; 4,76 MB
-
CapROS bear.png 99 × 88; 3 KB
-
Carbon-Black-Web.png 974 × 964; 34 KB
-
Cardboard “restricted viewing enclosure” -1.jpg 3264 × 1836; 1,22 MB
-
Cardboard “restricted viewing enclosure” -2.jpg 3264 × 1836; 1,59 MB
-
CC Paquet exigences fonctionnelles.jpg 714 × 1088; 57 KB
-
Chaos Communication Camp 2007 - ftp telnet tshirt.JPG 3456 × 2304; 4,07 MB
-
Cible De Sécurté Complétée.jpg 666 × 455; 52 KB
-
CibleDeSecurtéCC.png 828 × 566; 43 KB
-
CibleDeSecurtéComplétée.png 666 × 455; 260 KB
-
ClearShot diagram.png 789 × 262; 14 KB
-
Click'n'prove project view.png 1260 × 973; 44 KB
-
Click'n'prove proof interaction.png 1260 × 973; 35 KB
-
Cloud Computing (6648686983).jpg 350 × 248; 36 KB
-
Clé Initialisation.jpg 1280 × 960; 39 KB
-
Cmapimage1.jpg 6400 × 3496; 569 KB
-
CMM Question Example.png 558 × 170; 7 KB
-
CMM Question.png 361 × 133; 4 KB
-
CMM Structure.jpg 1221 × 621; 77 KB
-
CNSA 2p0 timeline.png 2226 × 1244; 674 KB
-
Common Criteria evaluation costs.png 699 × 373; 6 KB
-
Complexité mot de passe.png 800 × 600; 76 KB
-
Computer locked.jpg 500 × 710; 91 KB
-
Computer-security-emergency-response-process(high-res).png 2601 × 5307; 233 KB
-
Computer-security-incident-initial-process(high-res).png 2364 × 5182; 121 KB
-
Computer-security-incident-initial-process.png 379 × 830; 15 KB
-
Computersicherheit.jpg 1729 × 1214; 155 KB
-
ContentSecurityPolicy3 diagram.png 723 × 790; 61 KB
-
Contremesure.png 1256 × 782; 36 KB
-
Cookie-cooking-de.svg 198 × 108; 2 KB
-
Cookieeee.png 684 × 441; 92 KB
-
Cryptors Website.png 1352 × 675; 74 KB
-
CS5L CMM in mature CS approach.png 606 × 432; 43 KB
-
CS5L in mature approach cycle.png 813 × 613; 130 KB
-
CSKSRC.jpg 745 × 237; 64 KB
-
Cyber Assessment Tool Inherent Profile Layout.jpg 1235 × 389; 94 KB
-
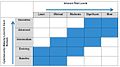
Cyber Assessment Tool Maturities.jpg 483 × 431; 30 KB
-
Cyber Assessment Tool Maturity.jpg 1252 × 531; 129 KB
-
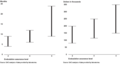
Cyber Assessment Tool risk maturity relationship.jpg 1105 × 620; 69 KB
-
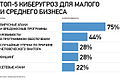
Cyber threats for small and medium businesses.jpg 660 × 444; 80 KB
-
Cyber threats in Russia.jpg 660 × 443; 104 KB
-
Cyber word bubble.png 512 × 395; 75 KB
-
Cyber-Versicherung-Vereine.png 581 × 471; 36 KB
-
Cyberciege.jpg 750 × 600; 52 KB
-
Cybersecurity 5-16 (5734032545).jpg 4288 × 1833; 3,68 MB
-
Cybersecurity 5-16 (5734032889).jpg 3035 × 2285; 3,06 MB
-
Cybersecurity 5-16 (5734033339).jpg 3506 × 2516; 3,88 MB
-
Cybersecurity 5-16 (5734034689).jpg 2367 × 2848; 2,93 MB
-
Cybersecurity 5-16 (5734035611).jpg 4288 × 2848; 5,01 MB
-
Cybersecurity 5-16 (5734038345).jpg 3894 × 2848; 4,77 MB
-
Cybersecurity 5-16 (5734039239).jpg 4288 × 2009; 3,98 MB
-
Cybersecurity 5-16 (5734039973).jpg 4288 × 2716; 5,13 MB
-
Cybersecurity 5-16 (5734040837).jpg 4288 × 2848; 5,19 MB
-
Cybersecurity 5-16 (5734583756).jpg 4288 × 2848; 5,01 MB
-
Cybersecurity 5-16 (5734584178).jpg 2331 × 2848; 2,96 MB
-
Cybersecurity 5-16 (5734586220).jpg 2120 × 2848; 2,53 MB
-
Cybersecurity 5-16 (5734586514).jpg 4288 × 2028; 4,11 MB
-
Cybersecurity 5-16 (5734587238).jpg 4288 × 2848; 4,97 MB
-
Cybersecurity 5-16 (5734588596).jpg 1804 × 2344; 2,06 MB
-
Cybersecurity 5-16 (5734591378).jpg 4288 × 2530; 5,17 MB
-
Cybersecurity and Infrastructure Security Agency.jpg 1157 × 803; 96 KB
-
Cybersecurity are you ahead of the curve? (39751718490).jpg 7360 × 4912; 5,27 MB
-
Cybersecurity are you ahead of the curve? (39751721520).jpg 7360 × 4912; 5,02 MB
-
Cybersecurity are you ahead of the curve? (39751729960).jpg 7360 × 4912; 5,18 MB
-
Cybersecurity Operations at Port San Antonio.jpg 2048 × 1152; 423 KB
-
Cybersecurity Strategy 5 Layer CS5L.png 585 × 601; 65 KB
-
Cybersecurity Strategy 5 layer CS5L.png 585 × 600; 66 KB
-
CyberSecurity Strategy CS5L Capability Maturity Model CMM Steps.png 548 × 240; 22 KB
-
Cybersecurity Strategy CS5L Capability Maturity Model CMM.jpg 1072 × 955; 111 KB
-
Cybersecurity Visuals Challenge 2019 - Afsal cmk.jpg 770 × 578; 23 KB
-
Cybersecurity Visuals Challenge 2019 - John Hurley.png 887 × 514; 34 KB
-
Cybersecurity Visuals Challenge 2019 - Rebecca Wang.jpg 770 × 555; 31 KB
-
Cybersecurity.png 8000 × 4500; 1,61 MB
-
Cyberstorm.mu team picture.jpg 1600 × 960; 283 KB
-
Cycle PCA.svg 319 × 213; 6 KB
-
Cyfirma Intro.jpg 1406 × 797; 186 KB
-
CYFIRMA's Cyber Security Controls Overview.png 800 × 678; 198 KB
-
Damo package.jpg 3648 × 2736; 1,68 MB
-
Damo penta.jpg 2448 × 3264; 1,99 MB
-
Danielle Fieseler works on a cybersecurity risk posture project.jpg 4928 × 3264; 1 MB
-
Data Flow Diagram - Online Banking Application.jpg 728 × 546; 80 KB
-
DC Spy Museum - Aurora Vulnerability Exhibit.jpg 3024 × 4032; 1,93 MB
-
De Surelock Phishing infographic.pdf 3593 × 11 516; 536 KB
-
Death Threat Email.png 1173 × 507; 89 KB
-
DEF CON 14 - Strom Carlson - Hacking FedEx Kinko's - How Not To Implement Stored-Value Card Systems.webm 47 min 16 s, 720 × 480; 109,13 MB
-
Demyo, Inc.jpg 320 × 180; 10 KB
-
Desktop in c drive.jpg 1366 × 768; 74 KB
-
DETERRENCE AND CYBER-WEAPONS (IA deterrenceandcyb1094532836).pdf 1275 × 1650, 88 stron; 623 KB
-
Development Center of TEC Solutions Limited.jpg 450 × 306; 230 KB
-
Diagram of a security descriptor for a file on Windows.png 916 × 736; 86 KB
-
Diagramma.png 574 × 297; 17 KB
-
Diagramme ArchiEmulateur.png 1254 × 987; 168 KB
-
Diagramme ArchiHyperviseur.png 1254 × 858; 164 KB
-
Diagramme ArchiIsolateur.png 1250 × 849; 133 KB
-
Diagramme ArchiKernelUserSpace.png 1250 × 779; 105 KB
-
Differential power analysis translate fr.png 713 × 563; 88 KB
-
Differential power analysis.svg 713 × 563; 264 KB
-
Disabling 2FA on Wikipedia.webm 16 s, 1488 × 820; 2,1 MB
-
Distance bounding protocol of Brands and Chaum.png 960 × 720; 10 KB
-
EBIOS-Modules.jpg 246 × 287; 38 KB
-
EFSOperation ja.jpg 1203 × 1599; 169 KB
-
EFSOperation.svg 1200 × 1600; 255 KB
-
Enclave.JPG 480 × 377; 31 KB
-
Endpoint.JPG 598 × 326; 41 KB
-
Engagement-dojo.png 2656 × 1372; 316 KB
-
EvilTwinWireless.jpg 550 × 389; 29 KB
-
Fabric Of Security Aechitecture (FOSA).jpg 746 × 402; 102 KB
-
FalcoArchitecture.png 767 × 363; 408 KB
-
FOC-Layered-Architecture-02.png 846 × 408; 33 KB
-
Fork bomb.svg 1300 × 800; 122 KB
-
Formato cella generica.png 456 × 117; 16 KB
-
Fotogramma video TC.png 768 × 576; 1,27 MB
-
Freedom Hosting Tor.jpg 1117 × 762; 63 KB
-
Function Hooking.svg 450 × 550; 22 KB
-
Gameofhacking.jpg 3024 × 4032; 2 MB
-
-
Garg Brothers inside view.jpg 4040 × 2246; 1,68 MB
-
GCSC-at-PPF-2019-945px.jpg 945 × 236; 144 KB
-
GCSC-at-PPF-2019.jpg 1400 × 350; 124 KB
-
GerixWifiCracker.png 660 × 674; 93 KB
-
Google Developer Group (Developer Festival) 01.jpg 1080 × 1080; 38 KB
-
CYBERSECURITY- SETTING THE RULES FOR RESPONSIBLE GLOBAL CYBER BEHAVIOR (IA gov.gpo.fdsys.CHRG-114shrg96851).pdf 1275 × 1650, 57 stron; 296 KB
-
Graphiquemalware.jpeg 550 × 315; 24 KB
-
GraphUpdateSignature.png 637 × 759; 58 KB
-
Handshake TLS.png 861 × 868; 57 KB
-
HAR2009 Canonical logo.png 595 × 419; 976 KB
-
Hash function el.svg 520 × 352; 88 KB
-
Hashlink timestamping.svg 1265 × 550; 73 KB
-
HijackThis-logo.png 128 × 128; 13 KB
-
Hijaking.jpg 365 × 264; 9 KB
-
HistoriqueVirtual.png 695 × 130; 12 KB
-
HyperDbg-Diagram-Overview-HQ.png 883 × 1588; 1,74 MB
-
Hyperviseur multiple.png 516 × 121; 7 KB
-
Hyperviseur type 1 et 2.png 481 × 274; 10 KB
-
Identity fabric - connecting anyone to every service.png 3354 × 1390; 255 KB
-
Identity-concept.svg 1383 × 912; 32 KB
-
Idlescan 2.png 428 × 423; 37 KB
-
Idlescan.png 784 × 273; 63 KB
-
IDMEF-Schema.png 514 × 796; 105 KB
-
Ids hybride.png 1018 × 699; 18 KB
-
Information Flow Policy Confidentiality Lattice.png 415 × 402; 25 KB
-
Information Security Word Cloud.png 1920 × 1080; 606 KB
-
Inside Penta.jpg 3461 × 2334; 3,98 MB
-
Intellectual Property, Espionage, and Cryptography Triangle c.gif 1261 × 1142; 51 KB
-
IODEF-Schema.png 464 × 846; 48 KB
-
Iptablesfb.png 1280 × 1024; 59 KB
-
ISA-62443 Standard Series 2012.png 2929 × 2104; 245 KB
-
Isms framework.jpg 600 × 411; 67 KB
-
ISO27001 Asset Management.JPG 680 × 425; 24 KB
-
IThena Project Bar.png 2000 × 360; 296 KB
-
J-VIS gate J.svg 549 × 363; 32 KB
-
JAGS Congress of Colombia.png 478 × 521; 444 KB
-
JAP screenshot.png 493 × 467; 60 KB
-
Java Update virus.png 1366 × 768; 56 KB
-
Jonathan Weissman.png 790 × 799; 431 KB
-
K600i Bluejacked.jpg 300 × 384; 49 KB
-
Karoshi logo.png 89 × 72; 13 KB
-
KD SQLIA Classification 2010.png 1202 × 1650; 280 KB
-
Kdesu proper.png 397 × 258; 11 KB
-
Kdesudo.png 410 × 236; 25 KB
-
Kerkesa e regjistrit.jpg 620 × 233; 27 KB